10 cyberattacks that exploited the principle of exposure
In the previous article (Information System security: understanding the issue of exposure), we highlighted the exposure of services on the internet, its origin, and the associated risks. In this article, we revisit ten cyberattacks that took advantage of the principle of exposure to succeed. Whether it was exploiting vulnerabilities, configuration defects, phishing techniques, or a combination of these different vectors, these are the elements that the targeted companies or investigative commissions were able to reveal following a post-mortem analysis of the attacks.
1 - Cisco, through an exposed VPN gateway
In May 2022, American network specialist Cisco discovered that they had been the victim of an attack and realized that some of their confidential files had been published on the dark web. The attacker compromised the Google account of one of the employees and extracted their login credentials and the VPN gateway address of the company's network. The attacker then used this access to connect to the network. They also bypassed the MFA mechanisms through a series of social engineering attacks against their victim.

Source: Cisco victime d'une cyberattaque (usine-digitale.fr)
2 - Okta, through an exposed VPN gateway
In January 2022, American identity management company Okta was hacked through a VPN access to Sykes, a subsidiary acquired in 2021. Attackers hijacked a user's credentials to authenticate themselves to the gateway. Once inside the network, they used classic exploitation and bouncing methods (disabling compromised computer's antivirus, stealing authentication tokens with Mimikatz, and exploiting passwords stored in plain text) to create an administrator account and persist within the information system.

Source: Le piratage d’Okta par Lapsus$ a été... une vraie promenade de santé (01net.com)
3 - About 1,000 companies via an exposed VSA application vulnerability
In July 2021, attacks were launched against companies using the VSA application, which manages IT infrastructures and is published by American company Kaseya. The attack exploited a critical vulnerability that affects the application, allowing attackers to bypass the platform's authentication and then spread ransomware within the infrastructures of over 1,000 Kaseya's clients. One of the remedies adopted was to remove VSA application exposure from the internet by shutting it down. Within 48 hours, 2,200 VSA instances disappeared from the internet, while 140 were still exposed.
Source: Le ransomware REvil s'attaque aux clients de Kaseya - Le Monde Informatique
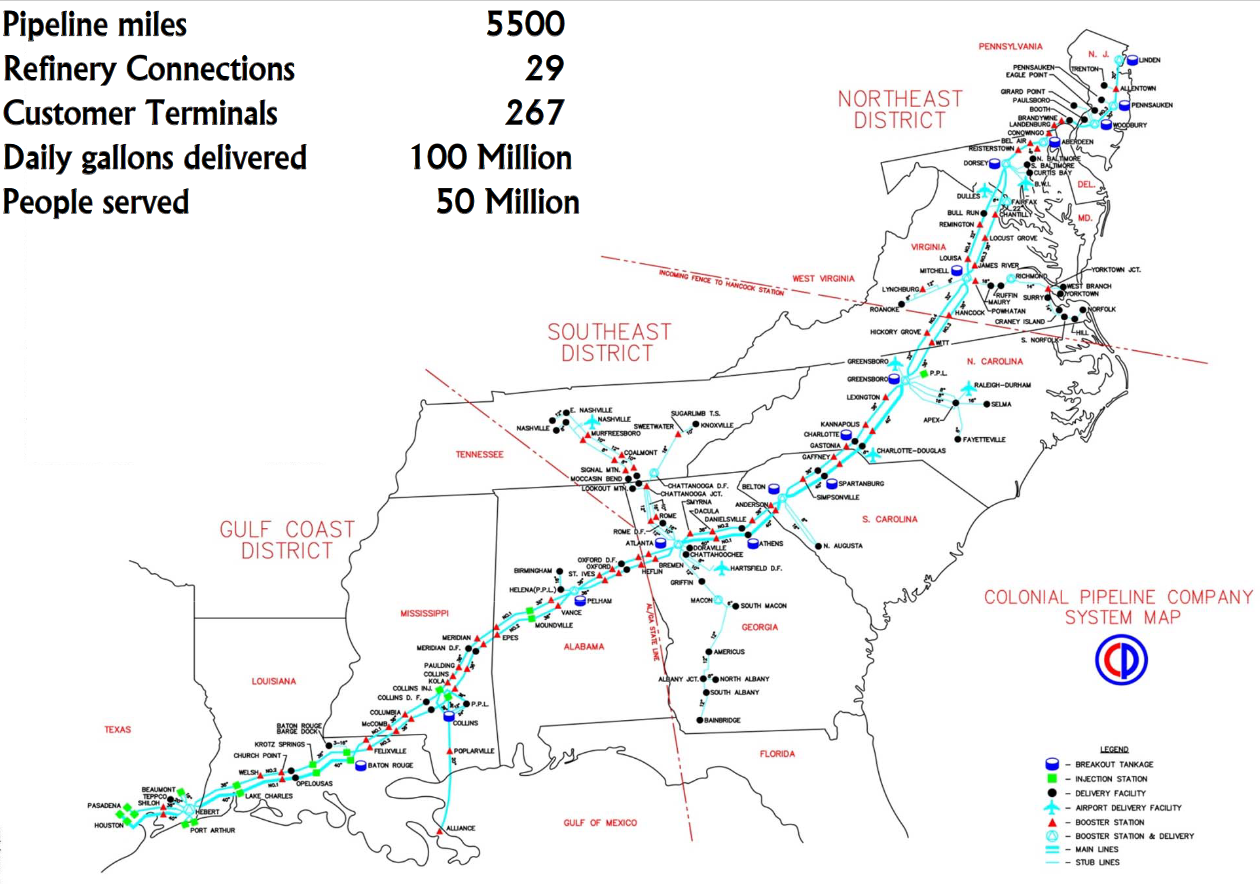
4 - Colonial Pipeline, through an exposed VPN gateway
In May 2021, the network of Colonial Pipeline, which transports 45% of all fuel on the East Coast of the United States, was hacked. The attacker entered through an exposed VPN gateway on the internet, reusing credentials that an employee had provided on another service.
Ransomware was propagated within the network, forcing the company to shut down the pipeline to avoid any further escalation by the attackers. Nearly 100 gigabytes of data, which the attackers threatened to publish, were also stolen. After several days of service interruption and a fuel shortage, the company paid the $4.4 million ransom demanded by the hackers.
Source: Mandiant: Compromised Colonial Pipeline password was reused | TechTarget
5 - Travelex, through an exposed VPN gateway
On New Year's Eve 2019, British currency exchange company Travelex, which operates in 70 countries, was hit by a cyber attack. The attacker exploited a vulnerability in the unpatched Pulse Connect Secure VPN gateway exposed on the company's internet. The vulnerability allowed an attacker to disclose technical information and bypass the gateway's authentication to connect to the network.
The vulnerability continued to be widely exploited in numerous attacks worldwide for several years after the patch was released by the vendor.

Source: ThreatAware | Discover and Protect Cyber Assets
6 - Over 300,000 machines in 150 countries, via SMB service exposure
In May 2017, the Wannacry ransomware exploited a vulnerability affecting SMB services of vulnerable exposed Windows Servers on the internet. The worm scanned the internet and infected machines' internal networks to detect vulnerable targets, then replicated itself by forcing the service to execute arbitrary code remotely. This vulnerability, called EternalBlue, was made public after a data leak from the NSA. The agency had developed a software exploit that was part of its offensive cybersecurity arsenal.
Source: Ce que l'on sait de cette cyberattaque colossale au niveau mondial (latribune.fr)
7 - Over 250,000 machines worldwide, via Microsoft Exchange server exposure
In January 2021, four zero-day vulnerabilities affecting on-premise Exchange servers were discovered and used by attackers to launch massive attacks through the associated exposed services on the internet. The chain of vulnerabilities allows attackers to bypass authentication mechanisms, elevate their privileges to administrator level, and deploy web shells.

Source: Here's what we know so far about the Microsoft Exchange hack | CNN Business
8 - Over 3,000 ESXi hypervisors, via SLP service exposure
In February 2023, a critical vulnerability affecting the Service Location Protocol (SLP) used by VMWare ESXi hypervisor for monitoring is discovered. The vulnerability allows an attacker capable of establishing a connection with the service to remotely execute code and take control of the machine. A wave of ransomware attacks exploiting this vulnerability is launched, infecting over 3,000 machines.
Source: Over 83,000 ESXi servers are internet-exposed as mass attack continues (thestack.technology)
9 - SolarWinds, through an exposed FTP server
In December 2020, a large-scale cyber attack affecting numerous US state services and 33,000 companies worldwide is detected. Attackers hacked the American software publisher of network supervision software SolarWinds and infected the Orion product as part of a supply-chain attack. The attackers authenticated themselves with an FTP service exposed on the internet by the company, using leaked credentials published on GitHub.

Source: SolarWinds Exposed GitHub Repository Publicly since 2018 (savebreach.com)
10 - The biggest DDoS in history, via 145,000 exposed cameras
In September 2016, French hosting provider OVH suffered the largest referenced distributed denial of service (DDoS) attack in history (nearly 1 Tb/s). The company's infrastructure held up against traffic from 145,000 IP cameras turned into zombie machines. A month later, DynDNS was hit by a similar attack, which slowed down access to many internet services including Twitter, PayPal, and Spotify. Connected objects, accessible through default, manufacturer-referenced credentials, or often affected by critical vulnerabilities, are a favorite target for hackers creating botnets who often only need to scan the internet for these exposed devices.
Sources :
- Attaque DDoS: un botnet de caméras de sécurité lâche 1 Tb/s contre OVH - Les Numériques (lesnumeriques.com)
- Attaque contre DynDNS, DDOS et IoT : comment se protéger ? Réponses d'experts - ZDNet
- Des caméras IP chinoises à l'origine de la gigantesque attaque DDoS - Le Monde Informatique
In the next article, we will discuss three common ways that companies try to solve the exposure problem. Sign up for the newsletter to not miss the next posts on the subject..